What is a distributed application?
Distributed applications (distributed apps) are applications or software that run on multiple computers within a network at the same time and can be stored on servers or cloud computing platforms. Unlike traditional applications that run on a single system, distributed applications run on multiple systems simultaneously.
Distributed applications run on distributed computing systems, which are a collection of independent computers that appear to the user as a single system. Computers in a distributed system operate concurrently and fail independently. They’re also asynchronous — meaning there’s no synchronization between their internal clocks. In addition to networks or cloud platforms, many distributed applications are also built and deployed on blockchain-based platforms.
Distributed apps are more resistant to certain cyber attacks because they have no single point of failure.
How do distributed apps work?
Distributed apps can communicate with multiple servers or devices on the same network from any geographical location. The distributed nature of the applications refers to data being spread out over more than one computer in a network.
Distributed applications are broken up into two separate models — the client software and the server software. The client software or computer accesses the data from the server or cloud environment, while the server or cloud processes the data. Cloud computing can be used instead of servers or hardware to process a distributed application’s data or programs. If a distributed application component goes down, it can failover to another component to continue running.
Distributed applications enable multiple users to access the apps at once. Many developers, IT professionals or enterprises choose to store distributed apps in the cloud because of its elasticity and scalability, as well as its ability to handle large applications or workloads. The cloud itself is based on distributed computing.
Enterprises can use container technology, such as Docker, to package and deploy distributed applications. The containers can build and run distributed applications, as well as separate distributed apps from other applications in a cloud or shared infrastructure.
Types of distributed app architecture
Distributed applications need to be hosted on more than one server to run. They rely on distributed systems, which are a network of machines that send and receive information spread out in different locations and organized into an architecture. Distributed apps can be organized into the following categories based on their underlying network architecture:
- Client-server. In a client-server architecture, multiple clients, or workstations, request resources such as shared files or printers from servers over the internet. Clients don’t provide resources to the server.
- Service-oriented architecture. In SOA, software components are made interoperable and reusable through service interfaces.
- Microservices architecture. A microservices architecture develops software systems in single-function modules and services, where each service is separately contained along with its data.
- Peer-to-peer. In a P2P architecture, there’s no central server and each node in the network has the same responsibilities. Blockchain uses a P2P network architecture.
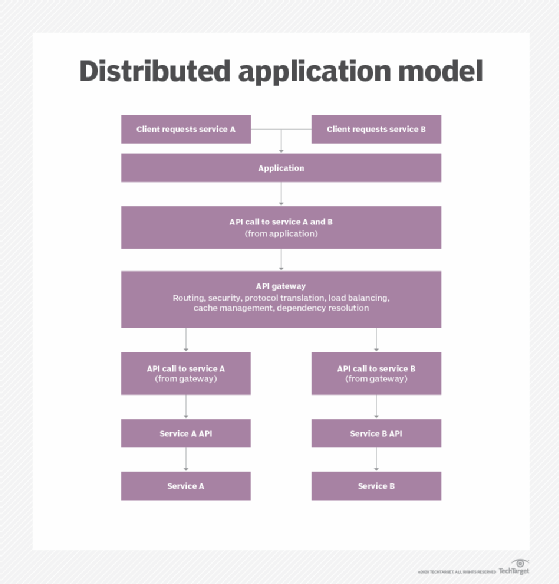
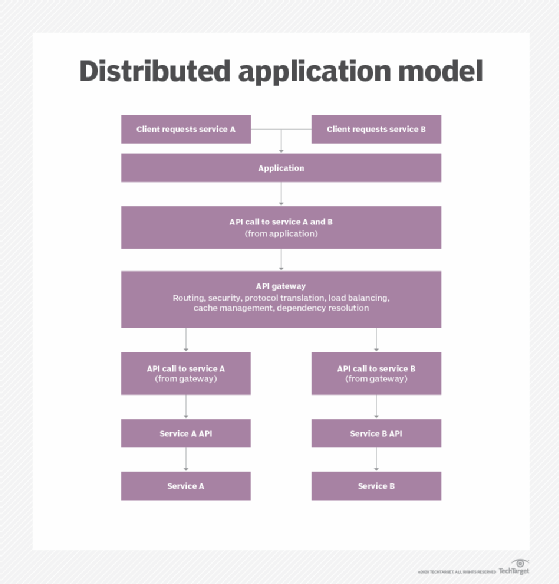
In client-server, server-oriented and microservices distributed architectures, nodes typically communicate via a broker — they don’t communicate directly. There’s an intermediary — often an application program interface (API) that handles routing of shared resources.
Examples of distributed applications
One example of a distributed application is an e-commerce platform that distributes different functions of the application to different computers in its network. The servers or computers host different functions, such as the following:
- Accept payment from customers at checkout.
- Update the customer list with new registrations.
- Answer customer questions using a chatbot.
- Accept product reviews from customers.
- Analyze customer history for targeted advertising.
Any application that produces data in one location and requires it in another physical location to function can be considered a distributed application. Distributed web applications are used in scenarios where fault tolerance, scalability and resource sharing are necessary.
Another example of a distributed application is the web browser Tor, which uses a distributed overlay network to anonymize Transmission Control Protocol-based applications.
Other examples of distributed applications include the following:
- banking applications;
- stock exchange applications;
- web browsers;
- streaming services;
- rideshare applications;
- food delivery applications; and
- massively multiplayer online games.
Operating systems (OSes) are another example of an application that can be distributed. Distributed OSes can be spread out over a collection of physically independent nodes that each handle a different job of the composite OS and are serviced by multiple CPUs.
How blockchain utilizes distributed applications
A blockchain is a distributed database that’s supported by and shared among multiple nodes in a computer network. Blockchains — like Bitcoin — are most commonly used as a distributed ledger for cryptocurrency transactions.
There are many types of blockchain, and some are used for holding different types of information, such as ledger entries and records. Ethereum, for example, is a blockchain that can be used to host other types of information, including application code. Distributed applications hosted on the blockchain are known as decentralized applications or dapps.
When decentralized apps are hosted on the blockchain, all the code is open source and all of the operations of the decentralized app are recorded into the immutable ledger. Anyone can access decentralized apps on the blockchain, but no single person owns the application. Decentralized apps on the blockchain are distributed and protected by encryption algorithms across the blockchain. There isn’t a central point of vulnerability for hackers to attack decentralized applications.
Decentralized apps on the blockchain may be indistinguishable on the front end from traditional applications and may be used for similar functions, but differ because of the way they’re hosted and use smart contracts.
Some examples of decentralized apps hosted on the blockchain — mostly Ethereum — include the following:
- Audius. A decentralized music streaming platform.
- EtherTweet. A decentralized blogging platform similar to Twitter.
- Golem Network. An open source decentralized supercomputer that’s freely accessible to anyone in the world. Users can rent out their computing power to others, creating a global network.
- Zed Run. A decentralized digital horse racing nonfungible token game that users can gamble on.
- Decentraland. A virtual reality platform that enables users to create avatars and buy and sell land.
Ethereum.org offers learning resources that teach dapp and software development on the blockchain.
Decentralized applications are a progression from distributed applications, where there isn’t a central server or data governance. Learn how this can be an asset for identity management in the enterprise.














